F5 WAF – Maximum Protection
If
you work as a security engineer, you’ll want the maximum protection
for your web services. However, the maximum protection requires more
administrative effort. It requires more knowledge about security and
more knowledge about the web services you are protecting. You’ll
get 90% of applications protected. It’s the maximum security level.
Nevertheless,
you’ll
have to work very hard. In
addition to configure all the security features of Good
Protection,
Elevated
Protection
and High
Protection,
you’ll have to configure Data Guard, DAST Integration, Protection
from parameter exploits (whitelisting) and Allowed HTTP request
methods.
The
best protection is blocking attacks in the inbound direction before
it can reach web servers. However, it may not be possible to detect
every inbound attack, and there may be some problematic outbound
traffic. Data
Guard
help us to protect outbound traffic. It examines outbound traffic for
patterns that match common sensitive data types, such
as credit card numbers or telephone numbers, and then masks the data
or blocks responses containing the data. It’s
an advanced security feature for customers who have concerns about
leaking sensitive data. If you enable Data Guard in your security
policy, by default, credit card and US social security numbers will
be masked.
 |
| Data Guard to mask sensitive data |
Many
organizations identify application security vulnerabilities using
automated tools such as Static Application Security Testing (SAST),
Dynamic Application Security Testing (DAST) or Run-time Application
Security Testing (RAST). The
BIG-IP ASM system is able to integrate with DAST and services from
providers like WhiteHat Security, HP, ImmuniWeb, Qualys, Quotium, and
Trustwave. DAST
integration
provides support for automated, closed-loop remediation of many
vulnerabilities identified by these tools. Therefore, the system
automatically customizes the security policy to resolve the
vulnerabilities.
 |
| Vulnerabilities found and verified by WhiteHat Sentinel |
Blacklisting
is a well-known security feature where there are signatures which are
malicious and have to be blocked. On
the other hand, whitelisting is a list of parameters which always
have to be allowed. Blacklisting
is easy to configure. However, whitelisting is hard to configure
because we have to know explicit parameters used by the application.
Whitelisting
provides more protection than blacklisting but it requires more
administrative effort because each time the application is modified,
the security policy have also to be modified.
 |
| Parameters List |
Finally,
Allowed HTTP
request methods
is another security feature for
a maximum protection. Most
web applications work with the GET and POST method. Therefore,
methods such as OPTIONS, DELETE, TRACE or HEAD are not used a lot.
Allowing only the GET and POST method is a best practice and
significantly reduce the security risk. The
BIG-IP ASM system can allow the GET and POST methods and block or
trigger a violation when other methods are used.
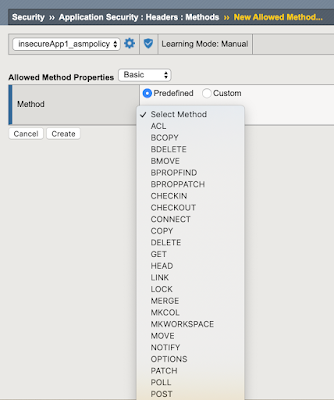 |
| Allowed HTTP Methods |
Regards!
You
already have all the security features ready for protecting your web
applications.










Commentaires
Enregistrer un commentaire